What is Web Alarm - Web Security Software to Monitor System Integrity?

Even one malicious change, can do harm to your IT infrastructures and exploit your data. Vulnerabilities in unsecured internet infrastructure, OS, application, and even user could end up doing damage to your reputation, someone’s career, and at worst decline the stock price data.
WebAlarm Security Monitoring was purposely built to protect your data from unauthorized changes as three-in-one solution for company IT infrastructure:
- Monitoring
- Protection
- Integrity
Not only securing, WebAlarm also evaluate and handle any suspicious changes that happened in your IT infrastructure.
Web content protection
Monitoring of web applications and data around the clock with automated recovery system.
Ensure web server integrity
Protecting web server from DNS records, settings, mail server configurations and controls data upload activities.
Provides data and application audit capability
Providing audit trails of file and data modifications.
What would you get by purchasing this product?
Extensive Auditing & Log Filtering Ability
Log file will serve as a forensic trail of hacker activity. All events such as file alteration alerts, file uploads, and modification details will be logged with each event tagged with a time and date.
WebAlarm log filtering ability will help by enabling quick filtering & easy search on specific log events.
Remote Administration
With the concept of Agent and Console, user can configure the agent only via console which can be installed locally to the agent or accessed remotely.
Multiple User Accounts

To maintain the WebAlarm Multiple user accounts with explicitly assigned permission can be created. Each WebAlarm agent will possess their own individual user account database allowing assignments of different administrative and normal user accounts.
Quick Response Time

WebAlarm integrity monitoring engine performs real-time surveillance on user selected files/folders. This enables instant detection of file modification and immediate restoration keeping downtime to a minimum.
Login Security

Admin user can restrict normal log on users & administrative account to a range of IP addresses. This practice makes it difficult for a foreign host within the internal network to pose as a valid host.
Backup Copy Monitoring

WebAlarm backup folder contains any backup copies of monitored files/folders which will be used by the agent to restore original files. The backup are monitored constantly retaining it’s authenticity. The backup copies are compressed or stored on a specified remote server to minimize disk space usage.
Secure Upload Feature

To update your website, upload modified files to the WebAlarm agent by allocating the admin user a specified amount of time to upload files. A scheduled upload feature allows website update to be on time with the selected schedule.
Here is the detailed features you will get
01. File & Data Integrity Monitoring
To ensure that your website is never successfully hacked, WebAlarm do a 24/7 protection efficiently and accurately to detect file modification. The Integrity check method are platform dependent with a variation in Windows and Unix. Each monitored file are checked for its existence, integrity, and access permissions.
WebAlarm will conduct backup procedure such as hashing to help with verifying file change detection. A brief illustration on event of unauthorized modification are as pictured


02. Automatic Recovery
WebAlarm provides 5 different website recovery options:
- Recovery
- No Recovery
- Alternative Page
- Update
- Log Monitoring
If you choose to recover the tampered files, WebAlarm will automatically take immediate action when detection confirmed that a specific file differs from the normal file, the agent then pulls the original file from the backup folder and replaces the altered copy with the original.
All monitoring and restoration process are done and logged without requiring any additional scripting by the administrator.
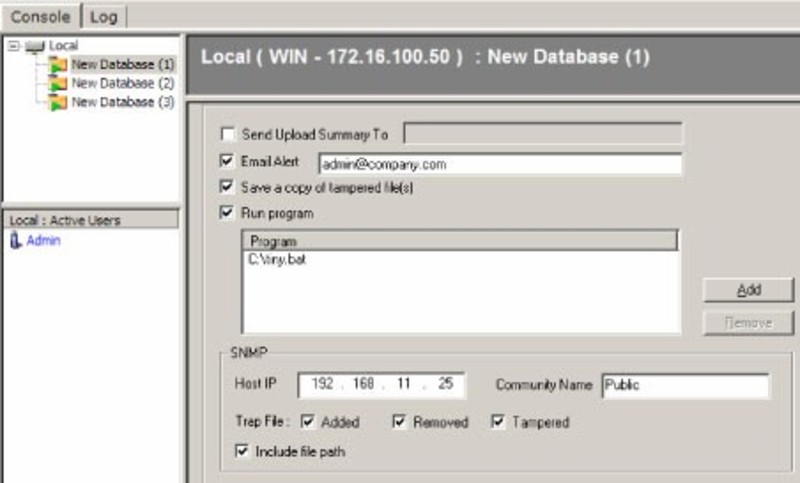
03. Data Violation Alert
WebAlarm Security Monitoring will issue alerts upon detection of any data integrity violation. The types of alerts include:
- console alerts
- network management console alerts
- via SNMP
- email alerts
- text message
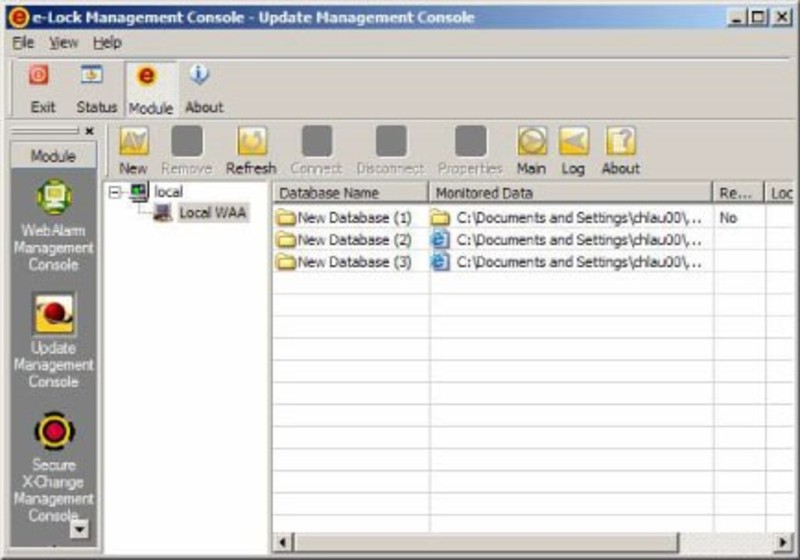
04. Data Update Management
WebAlarm continuously monitor your website without interruption while some part of the data is being updated. It provides 2 flexible methods for content owners to update the monitored data without triggering any false alarm.
- Secure scheduled update
- WebAlarm update module
You can choose whichever works best for you.
Example of Product Package
The Product
- WebALARM Professional Edition
- Volume Package (1 Console + Server Agents)
- include 1st Year Maintenance
Professional Service:
- Installation
- Service Support 8×5, 6 Tickets for Troubleshoot*
- 4 times Year Health Checks
*Fixes for general damage from misuse or to stabilize the software; if the request require to fix the system we will open the case to eLock as WebAlarm product principal.
Features:
- Monitoring
- Notification
- Recovery
- Graphical Management,
- Reporting
- Update Management Agent

